I’ve spent some time thinking about design of the authentication pages that we show to users when they (currently) sign in to Zendesk, Get Satisfaction, My Calendar or Linking You.
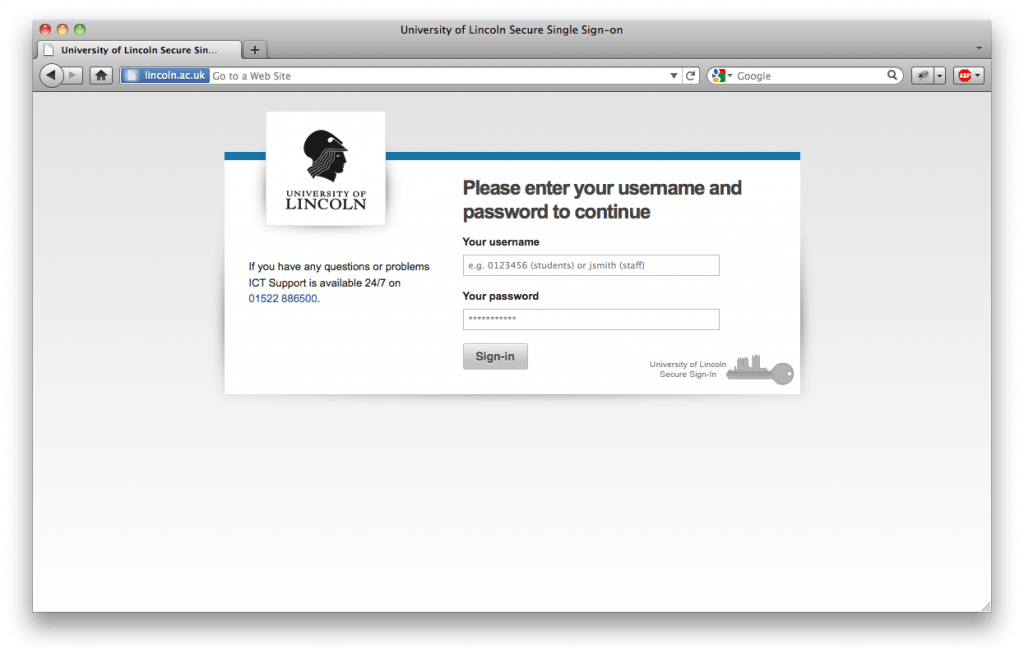
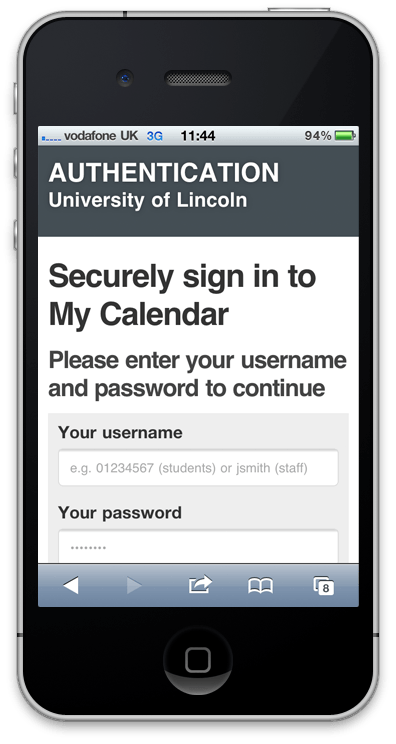
The current design uses a cut down version of the Common Web Design (CWD) v2.3. The main problem is that it doesn’t easily convert into a mobile design. Additionally, CWD v2.3 itself is full of cross browser hacks and lacks support for new browsers.
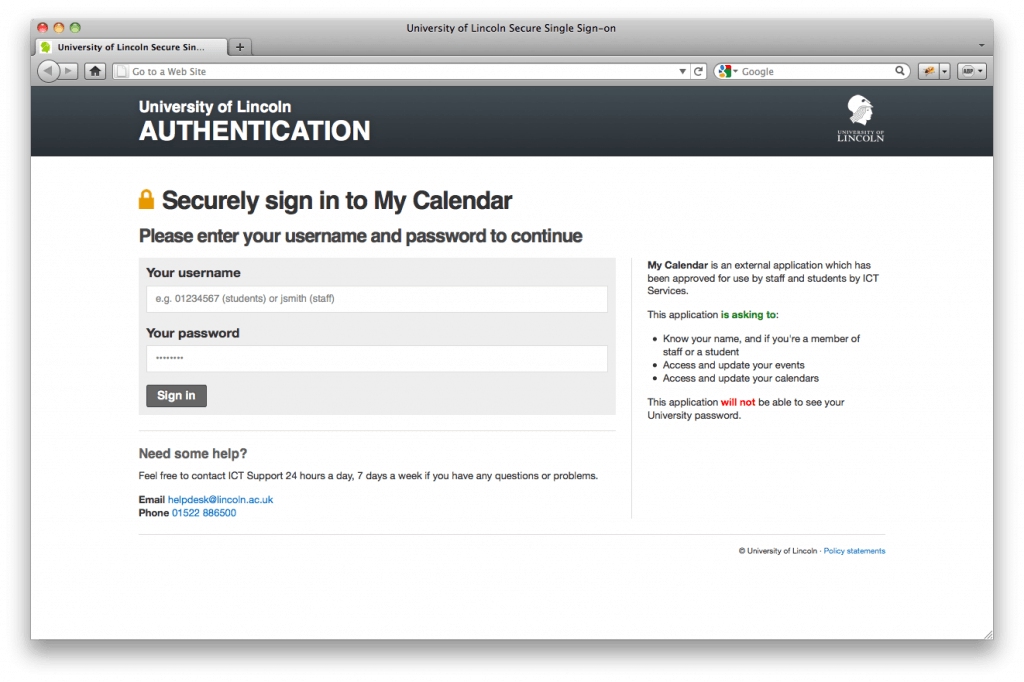
The proposed design uses our new 3.0 version of the CWD which has excellent browser and mobile support. With a move to OAuth 2.0 for more services, including Blogs and My Player (and hopefully Blackboard too), in the new academic year staff and students are going to be seeing this screens increasingly more and so for sign in screens for external applications I took a leaf out Facebook’s and Twitter’s books and a list of permissions that external applications are asking for.
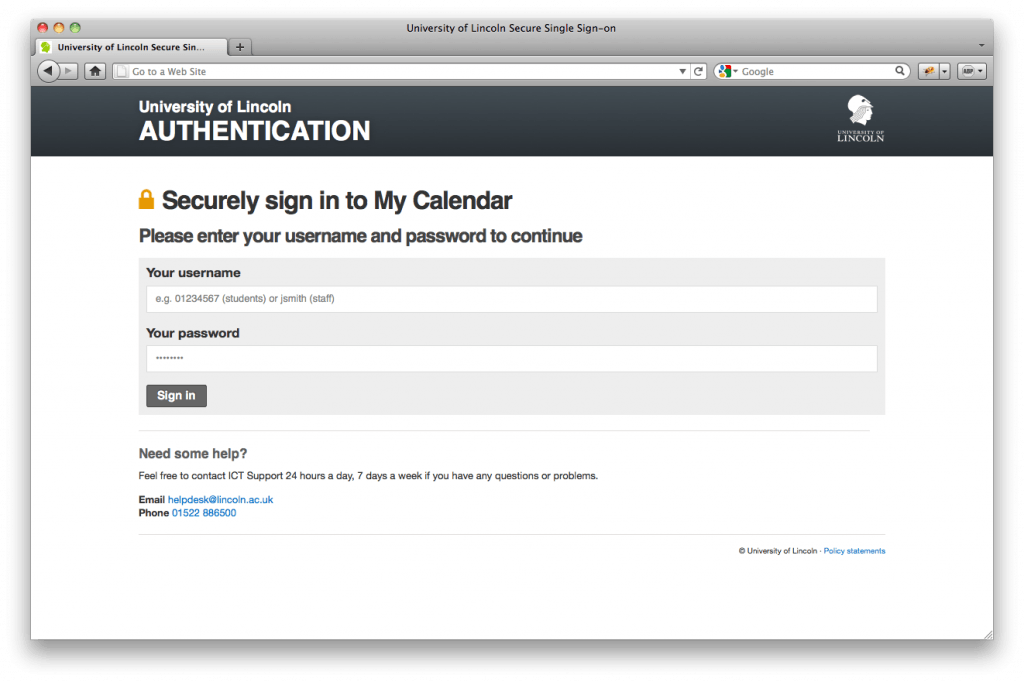
Internal application sign in will just feature a sign in form.
We are planning on updating the screens over the summer period.
What do you think?